Salesforce Security Model Tutorial
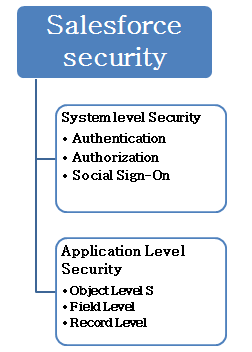
In Salesforce Security control is done by system level and Application Level Security. In this article we should able to get knowledge on security control in Salesforce. Salesforce Security is of two types they are
- System Level Security.
- Application Level Security.
System Level Security.
Authentication.
- Single Sign-On.
- Federated Authentication.
- Delegate Authentication.
Authorization.
- OAuth.
Social Sign –On.
- Twitter.
- Facebook.
- Sales force.
- Google.
- Janrain: provides 25+ different authentication users.
Application Level Security.
- Object Level Security.
- Field Level Security.
- Record Level Security.
Salesforce Security : Object Level
This object level Salesforce Security is also called as “Object Level Permission”. In this section we can control the data. Object Level security is one of the level of the security in salesforce in which we provide or access controlled permission to the prescribed user. Object level security can have the following features.
- We can prevent the user from editing, seeing, creating, deleting and managing a particular type of object.
- We can hide the entire TAB from a user.
Object Level security can be done in the following Sections.
- Permission Sets.
- Profiles
Permission Sets : In this Permission sets we define the access level of the user. Generally we determine what a user can do in the applications. These are used to grant additional permission to a user. Profiles : In Object level Security, Profiles are assigned to the user by system administrator. A profile can be assigned to many users where as a user can have only one Profile.
Salesforce Security :- Field Level
Here we control the user to see, edit, delete of a particular field in the object. In some situation like if we want to grant access control over Object to a user but the user should not be able to access some particular fields in that objects then we go for Field Level Security.
Field Level Security can be controlled by Profiles and Permission sets.
= > Profiles.
- Page Layouts.
- IP Ranges.
- Login Hours.
- Desktop.
- Client Access.
= > Permission sets.
- App Permissions.
- Record Types.
- Tab Settings.
- Assigned Apps.
- Object Permissions.
- Field Level Security.
- Apex Classes
- Visual Force Pages
Salesforce Security :- Record Level .
After setting Object and Field Level Security the situation may arise like if a user is eligible to access a particular Record in a Object there we use this sharing method . This can be done by the following settings.
- Org Wide Defaults.
- Role Hierarchy.
- Sharing Rules.
- Manual Sharing.
- Criteria Based sharing.
Organization-wide-Level Security
Determining Organization wide Defaults is the first step in record level security. This is the most restrictive level of locking the data to a user. Here if we give Read-Only accessibility to a user then the user is only made to Read to a particular Record.
Role Hierarchy.
After setting Organization wide default setting next step is to make settings in Role Hierarchy. Here we can give wider access to a record s with role Hierarchy. In Role Hierarchy we create Role Hierarchies for a organization.
Sharing Rules.
Sharing Rules makes automatic exceptions to organization wide defaults settings for particular users in an organization. Sharing rules can be done by manual sharing, criteria based sharing and Apex managed sharing.
Declarative Features of Record level security.
- What objects can I access?
- What page layouts can I See?
- What fields can I Access?
- Which tabs can I view?
- Which records types can I see?
- Which Apex classes are accessible for me?
- Which Visualforce pages can I access?